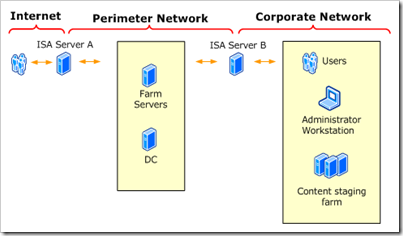
One of the most common extranet scenarios is the back-to-back perimeter model, wherein your entire SharePoint farm lives in the perimeter network with it’s own domain controller, while maintaining a trust relationship with the corporate network.
So, the next time someone asks you “What ports do I need open for Office SharePoint Server?” — Hopefully you can reference this.
Above is a loose diagram of the scenario I’m discussing. This is a simplified version of a drawing in Microsoft’s Extranet Topologies Document.
Between the Internet and the Perimeter network, the following must be available:
| Incoming | Outgoing | Port | Description |
| * | * | TCP 80 | Client Access |
| * | * | TCP 443 | Client Access (SSL) |
| * | TCP 25 | SMTP, Outgoing email | |
| * | * | TCP 56737, 56738 (SSL) | Office Server Web Services |
| * | TCP 135 + RPC Port | Single Sign-on Service |
Between the Corporate Network and the Perimeter network, the following must be available:
| Incoming | Outgoing | Port | Description |
| * | * | TCP 80 | Client Access |
| * | * | TCP 443 | Client Access (SSL) |
| * | TCP 25 | SMTP, Outgoing email | |
| * | TCP 80/443 | Content Publishing |
Additionally, to maintain a domain trust between corporate and perimeter domains you will need tcp/udp 135 (rpc), 389 (ldap), 636, 3268, 3269, 53 (dns), 88, 445 (ds), 789 (kerb)
Please let me know if you have any amendments to this from your experience, and I’ll add the information in!